I am using an external JavaScript lib in my chrome extension. I has inline execution, so I get following kind of error
(The error I get on console)
Refused to execute JavaScript URL because it violates the following Content Security Policy directive: "script-src 'self' chrome-extension://". Either the 'unsafe-inline' keyword, a hash ('sha256-...'), or a nonce ('nonce-...') is required to enable inline execution.
The error message clearly says there is a work-around possible.
Chrome-Content Security Policy says not possible. Many related question cited this link.
Blog This blogger says it is possible, but probably this is applicable to only older chrome extension.
Any work around possible?
PS: don't wanna/can't change the entire library I am using.
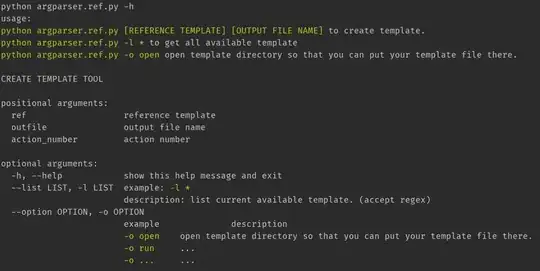
EDIT: how to use hash or nonce to enable inline execution.