Full transparency—I am by no means a Keycloak, OAuth, or OIDC expert and what I know is mostly from reading the docs, books, good ol' YouTube and playing around with the tool.
This post will be comprised of two parts:
- I'll attempt to answer all your questions to the best of my ability
- I'll show you all how you can play around with policies/scopes/permissions in Keycloak without needing to deploy a separate app in order to better understand some of the core concepts in this thread. Do note though that this is mostly meant to get you all started. I'm using
Keycloak 8.0.0.
Part I
Some terminology before we get started:
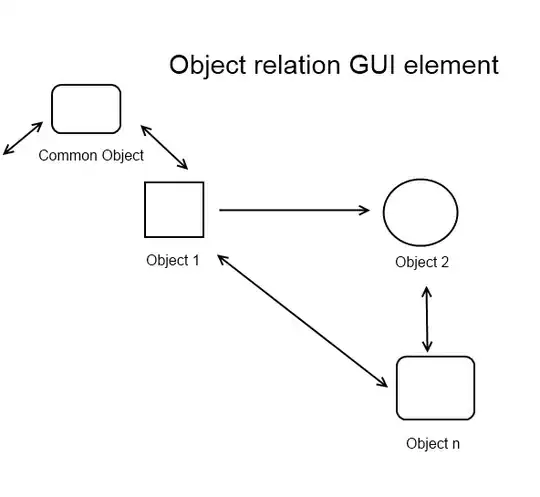
- In Keycloak, you can create two types of permissions: Resource-Based and Scope-Based.
- Simply put, for
Resource-Based permissions, you apply it directly to your resource
- For
Scoped-Based permission, you apply it to your scope(s) or scope(s) and resource.
is it best practice to create just one "view" scope, and use it across multiple resources (account, transaction, etc.)? Or should I create a "viewAccount" scope, a "viewTransaction" scope, etc.?
Scopes represent a set of rights at a protected resource. In your case, you have two resources: account and transaction, so I would lean towards the second approach.
In the long run, having a global view scope associated with all your resources (e.g., account, transaction, customer, settlement...) makes authorization difficult to both manage and adapt to security requirement changes.
Here are a few examples that you can check out to get a feel for design
Do note though - I am not claiming that you shouldn't share scopes across resources. Matter of fact, Keycloak allows this for resources with the same type. You could for instance need both viewAccount and viewTransaction scope to read a transaction under a given account (after all you might need access to the account to view transactions). Your requirements and standards will heavily influence your design.
For each practical combination of resource and scope, is it usual practice to create a permission?
Apologies, I don't fully understand the question so I'll be a bit broad. In order to grant/deny access to a resource, you need to:
- Define your policies
- Define your permissions
- Apply your policies to your permissions
- Associate your permissions to a
scope or resource (or both)
for policy enforcement to take effect. See Authorization Process.
How you go about setting all this up is entirely up to you. You could for instance:
Define individual policies, and tie each policy under the appropriate permission.
Better yet, define individual policies, then group all your related policies under an aggregated policy (a policy of policies) and then associate that aggregated policy with the scope-based permission. You could have that scoped-based permission apply to both the resource and all its associated scope.
Or, you could further break apart your permissions by leveraging the two separate types. You could create permissions solely for your resources via the resource-based permission type, and separately associate other permissions solely with a scope via the scope-based permission type.
You have options.
If there are multiple permissions matching a given resource/scope, what does Keycloak do?
This depends on
- The resource server's
Decision Strategy
- Each permission's
Decision Strategy
- Each policy's
Logic value.
The Logic value is similar with Java's ! operator. It can either be Positive or Negative. When the Logic is Positive, the policy's final evaluation remains unchanged. When its Negative, the final result is negated (e.g. if a policy evaluates to false and its Logic is Negative, then it will be true). To keep things simple, let's assume that the Logic is always set to Positive.
The Decision Strategy is what we really want to tackle. The Decision Strategy can either be Unanimous or Affirmative. From the docs,
Decision Strategy
This configurations changes how the policy evaluation engine decides whether or not a resource or scope should be granted based on the outcome from all evaluated permissions. Affirmative means that at least one permission must evaluate to a positive decision in order grant access to a resource and its scopes. Unanimous means that all permissions must evaluate to a positive decision in order for the final decision to be also positive. As an example, if two permissions for a same resource or scope are in conflict (one of them is granting access and the other is denying access), the permission to the resource or scope will be granted if the chosen strategy is Affirmative. Otherwise, a single deny from any permission will also deny access to the resource or scope.
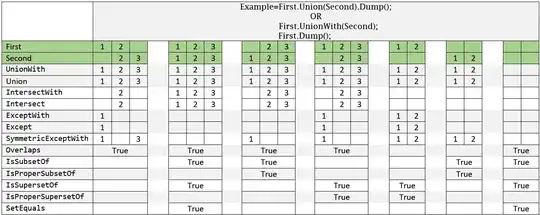
Let's use an example to better understand the above. Suppose you have a resource with two permissions and someone is trying to access that resource (remember, the Logic is Positive for all policies). Now:
Permission One has a Decision Strategy set to Affirmative. It also has 3 policies where they each evaluate to:
Permission Two has a Decision Strategy set to Unanimous with two policies:
- Now comes the final evaluation. If the resource server's
Decision Strategy is set to Affirmative, access to that resource would be granted because Permission One is true. If on the other hand, the resource server's Decision Strategy is set to Unanimous, access would be denied.
See:
We'll keep revisiting this. I explain how to set the resource sever's Decision Strategy in Part II.
so for example I could have permission to access "accounts" and permission for "view" scope, so therefore I would have permission to view accounts?
The short answer is yes. Now, let's expand on this a bit :)
If you have the following scenario:
- Resource server's
Decision Strategy set to Unanimous or Affirmative
- Permission to access the
account/{id} resource is true
- Permission to access the
view scope is true
You will be granted access to view the account.
true + true is equal to true under the Affirmative or Unanimous Decision Strategy.
Now if you have this
- Resource server's
Decision Strategy set to Affirmative
- Permission to access the
account/{id} resource is true
- Permission to access the
view scope is false
You will also be granted access to view the account.
true + false is true under the Affirmative strategy.
The point here is that access to a given resource also depends on your setup so be careful as you may not want the second scenario.
But am I right that this means I need a policy for each of the legacy groups that a user could belong to?
I'm not sure how Keycloak behaved two years ago, but you can specify a Group-Based policy and simply add all your groups under that policy. You certainly do not need to create one policy per group.
For example, if I have a "help desk" role, then I need a "help desk membership" policy, which I could then add to the "viewAccount" permission. Is this correct?
Pretty much. There are many ways you can set this up. For instance, you can:
- Create your resource (e.g.
/account/{id}) and associate it with the account:view scope.
- create a Role-Based Policy and add the
helpdesk role under that policy
- Create a
Scope-Based permission called viewAccount and tie it with scope, resource and policy
We'll set up something similar in Part II.
Part II
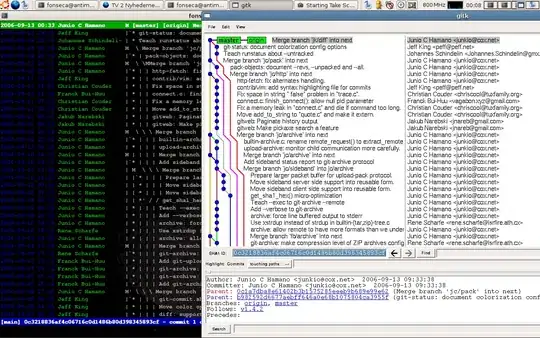
Keycloak has a neat little tool which allows you test all your policies. Better yet, you actually do not need to spin up another application server and deploy a separate app for this to work.
Here's the scenario that we'll set up:
- We'll create a new realm called
stackoverflow-demo
- We'll create a
bank-api client under that realm
- We will define a resource called
/account/{id} for that client
- The
account/{id} will have the account:view scope
- We'll create a user called
bob under the new realm
- We'll also create three roles:
bank_teller, account_owner and user
- We will not associate
bob with any roles. This is not needed right now.
- We'll set up the following two
Role-Based policies:
bank_teller and account_owner have access to the /account/{id} resourceaccount_owner has access to the account:view scopeuser does not have access to the resource or scope
- We'll play around with the
Evaluate tool to see how access can be granted or
denied.
Do forgive me, this example is unrealistic but I'm not familiar with the banking sector :)
Keycloak setup
Download and run Keycloak
cd tmp
wget https://downloads.jboss.org/keycloak/8.0.0/keycloak-8.0.0.zip
unzip keycloak-8.0.0.zip
cd keycloak-8.0.0/bin
./standalone.sh
Create initial admin user
- Go to
http://localhost:8080/auth
- Click on the
Administration Console link
- Create the admin user and login
Visit Getting Started for more information. For our purposes, the above is enough.
Setting up the stage
Create a new realm
- Hover your mouse around the
master realm and click on the Add Realm button.
- Enter
stackoverflow-demo as the name.
- Click on
Create.
- The top left should now say
stackoverflow-demo instead of the master realm.
See Creating a New Realm
Create a new user
- Click on the
Users link on the left
- Click on the
Add User button
- Enter the
username (e.g., bob)
- Ensure that
User Enabled is turned on
- Click
Save
See Creating a New User
Create new roles
- Click on the
Roles link
- Click on
Add Role
- Add the following roles:
bank_teller, account_owner and user
Again, do not associate your user with the roles. For our purposes, this is not needed.
See Roles
Create a client
- Click on the
Clients link
- Click on
Create
- Enter
bank-api for the Client ID
- For the
Root URL enter http://127.0.0.1:8080/bank-api
- Click on
Save
- Ensure that
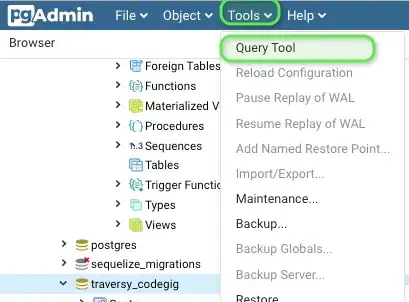
Client Protocol is openid-connect
- Change the
Access Type to confidential
- Change
Authorization Enabled to On
- Scroll down and hit
Save. A new Authorization tab should appear at the top.
- Click on the
Authorization tab and then Settings
- Ensure that the
Decision Strategy is set to Unanimous
- This is the resource server's
Decision Strategy
See:
Create Custom Scopes
- Click on the
Authorization tab
- Click on
Authorization Scopes > Create to bring up Add Scope page
- Enter
account:view in the name and hit enter.
Create "View Account Resource"
- Click on
Authorization link above
- Click on
Resources
- Click on
Create
- Enter
View Account Resource for both the Name and Display name
- Enter
account/{id} for the URI
- Enter
account:view in the Scopes textbox
- Click
Save
See Creating Resources
Create your policies
- Again under the
Authorization tab, click on Policies
- Select
Role from the the Create Policy dropdown
- In the
Name section, type Only Bank Teller and Account Owner Policy
- Under
Realm Roles select both the bank_teller and account_owner role
- Ensure that
Logic is set to Positive
- Click
Save
- Click on the
Policies link
- Select
Role again from the Create Policy dropdown.
- This time use
Only Account Owner Policy for the Name
- Under
Realm Roles select account_owner
- Ensure that
Logic is set to Positive
- Click
Save
- Click on the
Policies link at the top, you should now see your newly created policies.
See Role-Based Policy
Do note that Keycloak has much more powerful policies. See Managing Policies
Create Resource-Based Permission
- Again under the
Authorization tab, click on Permissions
- Select
Resource-Based
- Type
View Account Resource Permission for the Name
- Under
Resources select View Account Resource
- Under
Apply Policy select Only Bank Teller and Account Owner Policy
- Ensure that the
Decision Strategy is set to Unanimous
- Click
Save
See Create Resource-Based Permissions
Phew...
Evaluating the Resource-Based permission
Again under the Authorization tab, select Evaluate
Under User enter bob
Under Roles select user
- This is where we will associate our user with our created roles.
Under Resources select View Account Resource and click Add
Click on Evaluate.
Expand the View Account Resource with scopes [account:view] to see the results and you should see DENY.

This makes sense because we only allow two roles access to that resource via the Only Bank Teller and Account Owner Policy. Let's test this to make sure this is true!
Click on the Back link right above the evaluation result
Change bob's role to account_owner and click on Evaluate. You should now see the result as PERMIT. Same deal if you go back and change the role to bank_teller
See Evaluating and Testing Policies
Create Scope-Based Permission
- Go back to the
Permissions section
- Select
Scope-Based this time under the Create Permission dropdown.
- Under
Name, enter View Account Scope Permission
- Under
Scopes, enter account:view
- Under
Apply Policy, enter Only Account Owner Policy
- Ensure that the
Decision Strategy is set to Unanimous
- Click
Save
See Creating Scope-Based Permissions
Second test run
Evaluating our new changes
- Go back to the
Authorization section
- Click on
Evaluate
- User should be
bob
- Roles should be
bank_teller
- Resources should be
View Account Resource and click Add
- Click on
Evaluate and we should get DENY.
- Again this should come as no surprise as the
bank_teller has access to the resource but not the scope. Here one permission evaluates to true, and the other to false. Given that the resource server's Decision Strategy is set to Unanimous, the final decision is DENY.
- Click on
Settings under the Authorization tab, and change the Decision Strategy to Affirmative and go back to steps 1-6 again. This time, the final result should be PERMIT (one permission is true, so final decision is true).
- For the sake of completeness, turn the resource server's
Decision Strategy back to Unanimous. Again, go back to steps 1 through 6 but this time, set the role as account_owner. This time, the final result is again PERMIT which makes sense, given that the account_owner has access to both the resource and scope.