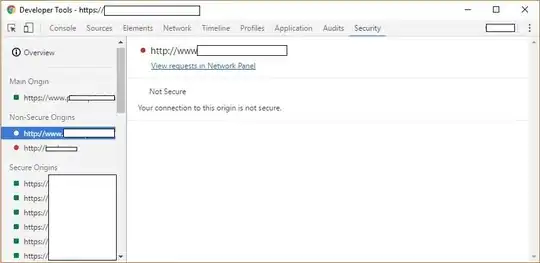
What's the most efficient way to find a list of all non-HTTPS URLs requested by an HTTPS page? If this kind of security violation happens, every browser alerts the user, but I can't find an easy way to find what exact URLs cause the violation.
The easiest way I've found so far is to use Firefox, but even then it's still not very convenient. First, I can right-click, select View Page Info, click the Media tab, and scroll through a list of URLs. However, this seems to only list image files, not CSS or JS includes that can also cause the error. For those, I have to use the Firebug extension, select the Net tab, and manually hover my mouse over each item to see the entire URL. Unfortunately, this can take a while if you have dozens of media files. Is there a better way?