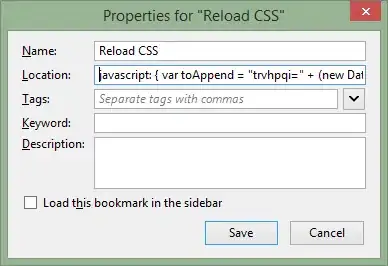
ANSWER: To anyone looking for this answer, I was able to get the token I needed by specifying the web API in the scopes of an MSAL acquireToken call, like so:
let token = msal.acquireToken({
scopes: [ 'myFunctionApp.azurewebsites.net/user_impersonation' ]
})
After doing this, I used the token as a Bearer token in the Authentication header. I'm able to use this in addition to calling MS Graph endpoints. I found this information in a quiet little out of the way place here:
Many thanks to @StanleyGong for his assistance that ultimately led to the answer.
/////
I've been looking for the past few days for how to effectively secure a Vue SPA served from an Azure Web App calling into an Azure Function App. I have Easy Auth turned on for both the web app and the function app and I'm calling the /.auth/me endpoint to get an id token, which I've read can be used as the bearer token. So what I'm doing is calling /.auth/me and using the returned id_token to create an Authorization header, but I still get a 401 Unauthorized when calling the function app.
Code getting the id_token from /.auth/me and adding it as a default header to all Axios calls (I do recognize that this will need to be refreshed...I'm going to create all that logic after I get a single call working):
let authUrl = '/.auth/me';
let response = await axios.get(authUrl);
let token = response.data[0].id_token;
axios.defaults.headers.common['Authorization'] = "Bearer " + token;
I can see the token being used in the Authorization header in the request, which immediately follows the section above:
Accept-Encoding: gzip, deflate, br
Accept-Language: en-US,en;q=0.9
Authorization: Bearer eyJ0eXAiO...
I saw this post and tried to use some of that info, including the blog post by Chris Gillum (which was helpful, but still didn't get me there): Authentication for Azure Functions
Any suggestions on how to get this working? I feel like I'm close, but I'm not quite there. If this isn't the right way to go about it, any advice would be helpful, too.
I'm horribly inexperienced at identity in general, so I keep getting turned around with the terminology which isn't helped by the inconsistency in documentation.
Also, is there any way to test this stuff without deploying code on every change? It would be great to test this by getting a token from the store somehow without the code being on the web app server...wishful thinking, I guess, but just wondering.
EDIT: I just realized that all the posts I've read suggest that an Access Token is returned from /.auth/me but I'm not getting one. The returned JSON looks like this, and this is all:
id_token: "eyJ0eXA...7_A"
provider_name: "aad"
user_claims: [{typ: "aud", val: "2...fa"},…]
user_id: "<<my email address>>"
ANOTHER EDIT: I've found I can get a token using MSAL but the info it contains is slightly different than that from /.auth/me. Using either token as the bearer token still results in a 401. I did notice that in the AAD auth setup for the apps that the issuer URL was different. One was sts.windows.net and the other was login.windows.net. Both had the tenant ID after them. Not sure if this made a difference, but I tried setting them to the same value and that didn't help.
/.auth/me token (sanitized, of course):
{
"aud": "2fe...fa", (AAD app id)
"iss": "https://sts.windows.net/<< AD tenant id >>/",
"iat": 15785xxx,
"nbf": 15785xxx,
"exp": 15785xxx,
"aio": "AVQAq/...UQ=",
"amr": [
"pwd",
"mfa"
],
"family_name": "<< my last name >>",
"given_name": "<< my first name >>",
"ipaddr": "<< my ip >>",
"name": "<< my full name >>",
"nonce": "e32a...48",
"oid": "a0...0e",
"sub": "LNu...8l8",
"tid": "f14...2ca",
"unique_name": "<< my email >>",
"upn": "<< my email >>",
"uti": "i9O...TAQ",
"ver": "1.0"
}
MSAL access token:
{
"aud": "000...000", (mostly 0s...not sure what this id is)
"iss": "https://sts.windows.net/<< AD tenant id >>",
"iat": 15785xxx,
"nbf": 15785xxx,
"exp": 15785xxx,
"acct": 0,
"acr": "1",
"aio": "AVQAq/8O...ZZ12s=", (different than above)
"amr": [
"pwd",
"mfa"
],
"app_displayname": "<< app name in AAD app registration >>",
"appid": "<< app GUID from AAD >>",
"appidacr": "0",
"family_name": "<< my last name >>",
"given_name": "<< my first name >>",
"ipaddr": "<< my ip >>",
"name": "<< my full name >>",
"oid": "a0...0e", (same as above)
"platf": "3",
"puid": "10...1B",
"scp": "User.Read profile openid email",
"signin_state": [
"kmsi"
],
"sub": "WuX...L3A",
"tid": "f14...2ca", (tenant id, same as above)
"unique_name": "<< my email >>",
"upn": "<< my email >>",
"uti": "UD...AA",
"ver": "1.0",
"xms_st": {
"sub": "LNu...8l8"
},
"xms_tcdt": 14...37
}