I have an EC2 instance running in AWS. When I try to ping from my local box it is not available.
How can I make the instance pingable?
I have an EC2 instance running in AWS. When I try to ping from my local box it is not available.
How can I make the instance pingable?
Add a new EC2 security group inbound rule:
A few years late but hopefully this will help someone else...
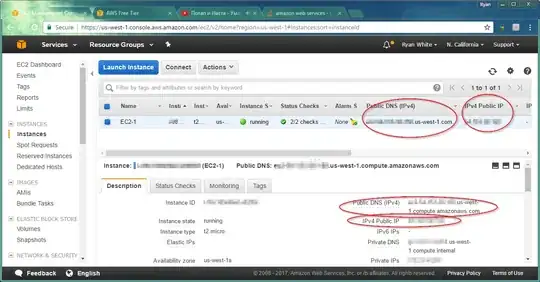
If has a Public DNS or Public IP address (circled below) then you should be good. This will be the address you ping.
Next make sure the Amazon network rules allow Echo Requests. Go to the Security Group for the EC2.
Note: Thank you santosh s for this one.
Your VPC is connected to a network and this network might have some ACLs blocking it also.
Next, Windows firewall blocks inbound Echo requests by default. Allow Echo requests by creating a windows firewall exception...
Done!
Hopefully you should now be able to ping your server.
You have to edit the Security Group to which your EC2 instance belongs and allow access (or alternatively create a new one and add the instance to it).
By default everything is denied. The exception you need to add to the Security Group depends on the service you need to make available to the internet.
If it is a webserver you will need to allow access to port 80 for 0.0.0.0/0 (which means any IP address).
To allow pinging the instance you need to enable ICMP traffic.
The AWS Web Console provides some of the most commonly used options in the relevant dropdown list.
The custom ICMP rule in the security group is not what it takes, a least for me. But the following rule will work:
Type: All ICMP
Protocol: TCP
Port range: 0 - 65535
Source: Anywhere - 0.0.0.0/0
After doing this you will be able to ping other instances. You should see something like:
PING 10.0.0.15 (10.0.0.15): 56 data bytes
64 bytes from 10.0.0.14: icmp_seq=1 ttl=64 time=3.9 ms
64 bytes from 10.0.0.14: icmp_seq=2 ttl=64 time=3.9 ms
64 bytes from 10.0.0.14: icmp_seq=3 ttl=64 time=10.6 ms
64 bytes from 10.0.0.14: icmp_seq=4 ttl=64 time=40.6 ms
64 bytes from 10.0.0.14: icmp_seq=5 ttl=64 time=3.8 ms
64 bytes from 10.0.0.14: icmp_seq=6 ttl=64 time=5.3 ms
64 bytes from 10.0.0.14: icmp_seq=7 ttl=64 time=6.5 ms
64 bytes from 10.0.0.14: icmp_seq=8 ttl=64 time=3.5 ms
64 bytes from 10.0.0.14: icmp_seq=9 ttl=64 time=21.0 ms
64 bytes from 10.0.0.14: icmp_seq=10 ttl=64 time=3.5 ms
64 bytes from 10.0.0.14: icmp_seq=11 ttl=64 time=3.5 ms
64 bytes from 10.0.0.14: icmp_seq=12 ttl=64 time=59.7 ms
64 bytes from 10.0.0.14: icmp_seq=13 ttl=64 time=3.5 ms
64 bytes from 10.0.0.14: icmp_seq=14 ttl=64 time=3.5 ms
64 bytes from 10.0.0.14: icmp_seq=15 ttl=64 time=4.8 ms
64 bytes from 10.0.0.14: icmp_seq=16 ttl=64 time=3.1 ms
64 bytes from 10.0.0.14: icmp_seq=17 ttl=64 time=3.1 ms
64 bytes from 10.0.0.14: icmp_seq=18 ttl=64 time=3.0 ms
64 bytes from 10.0.0.14: icmp_seq=19 ttl=64 time=3.1 ms
--- 10.0.0.14 ping statistics ---
20 packets transmitted, 19 packets received, 5% packet loss
round-trip min/avg/max = 3.0/9.9/59.7 ms
That´s it.
Please go through the below checklists
1) You have to first check whether the instance is launched in a subnet where it is reachable from the internet
For that check whether the instance launched subnet has an internet gateway attached to it.For details of networking in AWS please go through the below link.
public and private subnets in aws vpc
2) Check whether you have proper security group rules added,If notAdd the below rule in the security group attached to instance.A Security group is firewall attached to every instance launched.The security groups contain the inbound/outbound rules which allow the traffic in/out of the instance.by default every security group allow all outbound traffic from the instance and no inbound traffic to the instance.Check the below link for more details of the traffic.
Type: custom ICMPV4
Protocol: ICMP
Portrange : Echo Request
Source: 0.0.0.0/0

3) Check whether you have the enough rules in the subnet level firewall called NACL.An NACL is a stateless firewall which needs both inbound and outbound traffic separately specified.NACL is applied at the subnet level, all the instances under the subnet will come under the NACL rules.Below is the link which will have more details on it.
Inbound Rules . Outbound Rules
Type: Custom IPV4 Type: Custom IPV4
Protocol: ICMP Protocol: ICMP
Portrange: ECHO REQUEST Portrange: ECHO REPLY
Source: 0.0.0.0/0 Destination: 0.0.0.0/0
Allow/Deny: Allow Allow/Deny: Allow

4) check any firewalls like IPTABLES and disble for testing the ping.
1.Go to EC2 Dashboard and click "Running Instances" on "Security Groups"
2.select the group of your instance which you need to add security.
3.click on the "Inbound" tab
4.Click "Edit" Button (It will open an popup window)
5.click "Add Rule"
6.Select the "Custom ICMP rule - IPv4" as Type
7.Enter the "0.0.0.0/0" as Source or your public IP
7.Click "Save"
Those who are new to aws ec2 and wants to access the instance from SSH, Broswer, Ping from system then below is the inbound rule for these:-
Go to the security group of the EC2 instance and edit the inbound rule allow 0.0.0.0/0 for ICMP.
It will work.
If you want to enable ping (from anywhere) programmatically, via the SDK, the magic formula is:
cidrIp: "0.0.0.0/0"
ipProtocol: "icmp"
toPort: -1
fromPort: 8
For example, in Scala (using the AWS Java SDK v2), the following works to define an IpPermission for the authorizeSecurityGroupIngress endpoint.
val PingPermission = {
val range = IpRange.builder().cidrIp( "0.0.0.0/0" ).build()
IpPermission.builder().ipProtocol( "icmp" ).ipRanges( range ).toPort( -1 ).fromPort( 8 ).build()
}
(I've tried this is only on EC2-Classic. I don't know what egress rules might be necessary under a VPC)
Security groups enable you to control traffic to your instance, including the kind of traffic that can reach your instance.
1. Check the Security Groups (Enabled the PORTS to be OPEN)
2. Check the correct VPC
3. Attached the correct Subnet
4. AWS EC2 to be in Public Subnet
5. Enable Internet Gateway
Open the Ports in AWS EC2 check this link offical AWS link
I had a deeper problem--I had created a VPC, subnet, and appropriate Security Group, but neglected to add an Internet Gateway and associate it with my subnet. Since this is my first Google result for "Can't ping ec2", I'm posting this information here in case it proves useful to someone else (or myself in the future).
You have to open following security port in the security group. Each rule is for different purposes, as shown below.
ALL ICMP for ping.
HTTP for accessing URL on HTTP port.
HTTPS for accessing URL on Secured HTTP port.
As per your requirement you can change SOURCE
By default EC2 is secured by AWS Security Group (A service found in EC2 and VPC). Security Group by default are disallowing Any ICMP request which includes the ping. To allow it:
Goto: AWS EC2 Instance Locate: The Security Group bind to that instance (It's possible to have multiple security group) Check: Inbound Rules for Protocol (ICMP) Port (0 - 65535) if it's not present you can add it and allow it on your specified source IP or Another Security Group.
Go to your instance, edit your security group and edit inbound rules
NOTE: Make sure in the protocol you select Echo Request not Echo Reply
might be your internal network is blocking that IP to ping or blocked ping packet in your firewall if you have opened in security group and VPC is correct.
I tried multiple soulutions from above steps, but what worked for me is
changing the internet connection to my mobile hotspot
and trying again. Something on my home's internet settings was not allowing me to connect into RDP. Where as i was able to SSH to a linux servers
Yes you need to open up access to the port. Look at Security Groups http://docs.aws.amazon.com/AWSEC2/latest/UserGuide/using-network-security.html
Your EC2 instance needs to be attached to a security group that allows the access you require.
If you setup the rules as "Custom ICMP" rule and "echo reply" with anywhere it will work like a champ. The "echo request" is the wrong rule for answering pings.
When pinging two systems, by default SSH is enabled (if you have connected via putty or terminal.) To allow ping, I added the security group for each of the instance (inbound).
terraform specific instructions for a security group because the -1 was not obvious to me.
resource "aws_security_group" "Ping" {
vpc_id = "${aws_vpc.MyVPC.id}"
ingress {
from_port = -1
to_port = -1
protocol = "icmp"
cidr_blocks = ["0.0.0.0/0"]
ipv6_cidr_blocks = ["::/0"]
}
}
I had the same problem truying to connect from linux server to EC2, you have two make sure about to things that "ALL ICMP" is added from EC2 as shown above and that alone won't work, you have to update Ansible to newest version 2.4, it did not work with my previous version 2.2.
There are 2 things to consider.
Type: custom ICMPV4 , Protocol: ICMP , Portrange : Echo Request , Source: 0.0.0.0/0
Check firewall status of the EC2 instance. In /etc/ufw/before.rules append following
A ufw-before-input -p icmp --icmp-type echo-request -j ACCEPT
Make sure you are using the Public IP of you aws ec2 instance to ping.
edit the secuity group that is attached to your EC2 instance and add an inbound rule for ICMP protocol.
try pinging, if this doesnt fix, then add outbound rule for ICMP in the security group.
1-check your security groups
2-check internet gateway
3-check route tables
When accessing new ports in ec2 instance. You have add in 2 places. 1. Security group inbound ports. 2. Firewall settings inbound rules.
I will like to mention some rare ISP induced problems. Occasionally following happends to me with BSNL. its one of those wierd problems that takes hours out of your daily life. In such case one might raise the issue with ISP or change ISP.